Found attachment of size 1034123.
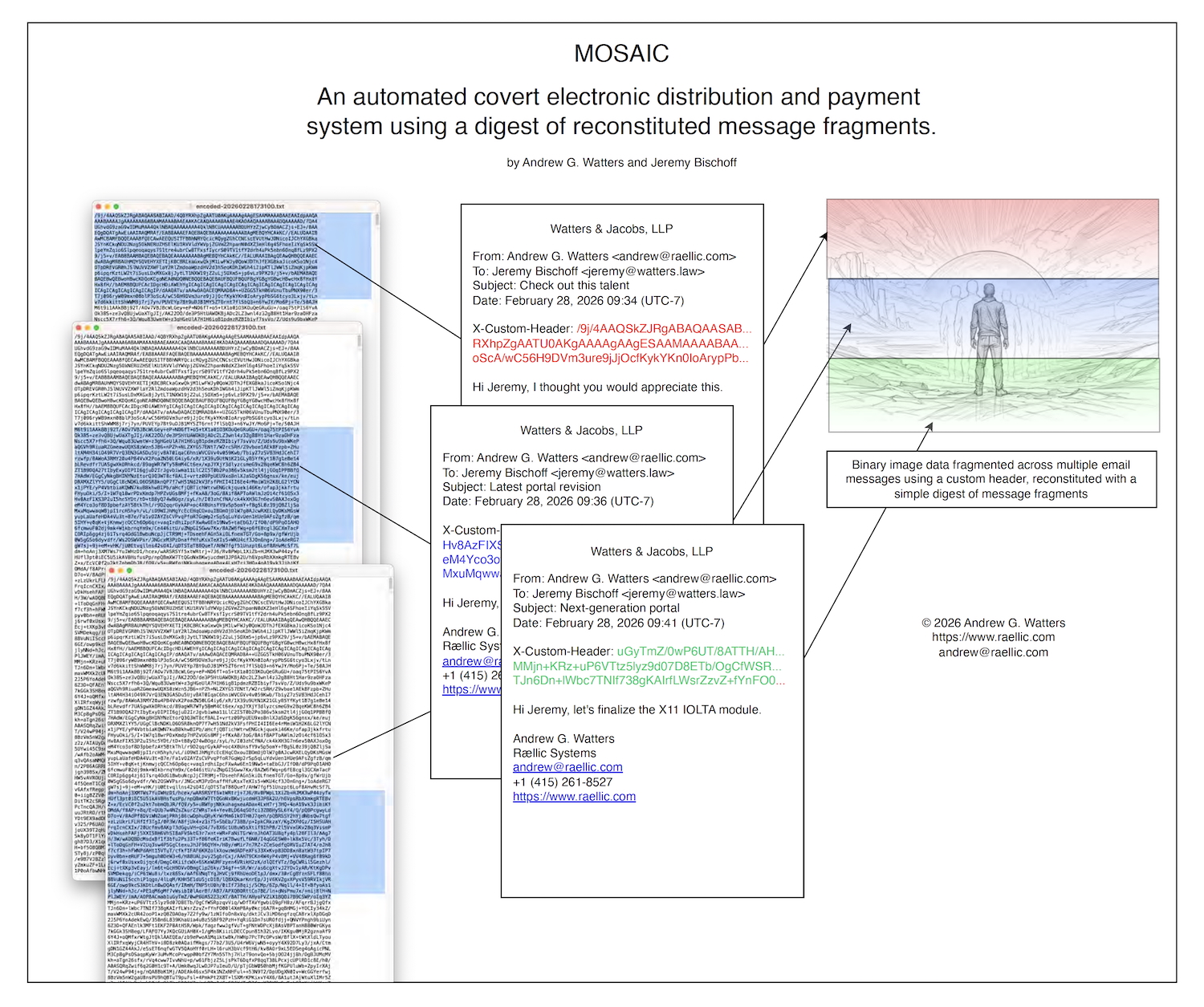
Sat, 28 Feb 2026 10:43:13 -0800 Andy from private IP, post #18269691 /all My greatest ever work: MOSAIC Announcing the discovery of a technique/system we're calling MOSAIC: An automated covert electronic distribution and payment system using a digest of reconstituted message fragments. All that is required is an email or XMPP server and you have an essentially undetectable platform for distributing CSAM and taking payments, both of which would be stored in a server-side queue, sent in pieces in custom email headers, and recorded in a blockchain ledger. This is a big deal because someone who doesn't have the app on the receiving end only sees a custom email header encoded in Base64, also encrypted. This is kind of like FreeNet, but easier to automate and harder to detect. Detection would depend on catching custom email headers in the raw source of the Epstein emails. The government has that and could easily do this with the #EpsteinFiles if they have the raw source. Ever wonder whether Hillary had custom headers set on her email server? That would be a good place to look, as well. #News #Programming #Technology Sun, 01 Mar 2026 07:36:04 -0800 Andy from private IP Reply #10854004 I updated the graphic to clean up a few things and add more. https://www.watters.law/articles/attachments/11-MOSAIC.pdf Sun, 01 Mar 2026 08:40:04 -0800 phosita from private IP Reply #17976678 👍 Why confine yourself to email headers? This just looks like a different flavor of stego to me. You could embed the Base64 stuff in one or more formats capable of holding it: (1) email, be it headers as you propose or body text itself; (2) binary images (various stego libs exist); (3) audio, using subaudible stuff you can exctract using DSP; and (4) so on. I strongly suspect that, but have not personally tested whether, #2 and #3 can be done in a way that survives transcoding. Seems to me the utility of what you have proposed is for establishing a covert channel of communication. An attacker has to: determine that cyphertext is being exchanged; determine what cyphertexts from the universe of known cyphertexts are the entirety of a message; assemble the cyphertexts correctly; and decrypt the cyphertext into plaintext. The limit of this is the ability of a sophisticated attacker - now or in the future - to reassemble and decrypt. This includes rubber hose cryptography. Not that there isn't utility in hiding the fact that you're sending cyphertext to someone. There is nonzero. Still security by obscurity though. Alice and Bob, using MOSAIC, must also arrive at a satisfactory solution to the problem of key exchange. I realize that's not the use case for MOSAIC. (Alice and Bob could use MOSAIC for key exchange, but then it's MOSAICs all the way down until at bedrock there's some non-MOSAIC key exchange.) Oh also MOSAIC as you've described it distributes *encrypted* partial cyphertext; but I suppose there's no inherent reason the stuff couldn't be plaintext either. See also ye olde BBS tech of using .par files. Also comes to mind various schemes for distributing a $foo among n people such that Sun, 01 Mar 2026 08:43:03 -0800 phosita from private IP Reply #17195120 ...huh...that got truncated. Buggy. Anyway such that "[less than symbol] n of them can reconstitute it." Think "we 9 are the group who sign the root certs; and any 7 of us can reconstitute the key." Sun, 01 Mar 2026 12:55:30 -0800 Andy from private IP Reply #16367873 Yes, it's not limited to email, but this is an ideal delivery platform since nobody is looking on port 25 for extra headers when most email servers have TLS connections anyway and the government isn't going to crack the encryption. Sure, in the old days of insecure email and Telnet, this wouldn't work, which is why it's timely now. I'm not talking about steganography in images, which is already well-known. This is a fragmentation approach that hides well in existing email traffic, which may be novel. I appreciate your insight, in any case. Fri, 06 Mar 2026 08:00:41 -0800 Andy from private IP Reply #13314694 We wrote an interactive shell script that does everything within one day of work. This is a very scary discovery. Fri, 06 Mar 2026 11:57:47 -0800 phosita from private IP Reply #15635851 Cool! You will release it to the community, yes? Fri, 06 Mar 2026 13:50:02 -0800 Andy from private IP Reply #11654262 Yes, will be published along with the white paper. Sat, 07 Mar 2026 07:41:13 -0800 Andy from private IP Reply #14221877 This is so good it's unbelievable. Here it is! https://www.watters.law/articles/attachments/mosaic/MOSAIC.pdf https://www.watters.law/articles/attachments/mosaic/mosaic.sh Sat, 07 Mar 2026 08:23:51 -0800 phosita from private IP Reply #18674056 👍 Reviewing the code presently. Sat, 07 Mar 2026 08:55:32 -0800 Andy from private IP Reply #16248234 Try it out on any small image file. It produces the emails with embedded fragments plus a report on what it did. One day of effort! Mon, 09 Mar 2026 09:57:24 -0700 phosita from private IP Reply #12373466 I tried it on a 1-GiB file of randomness. Some wonky results ensued. Have been, and am, kinda pressed for time. But some observations in no particular order: (1) using time, even to the nanos, as a unique identifier is not best practice. On Linux, a couple things come to mind instead. man uuidgen man urandom I do not have a macintosh, so can't tinker macintoshly, but I have (old) FreeBSD handy. I am less familiar with the RNG shit in FreeBSD, but that OS ships with uuidgen as well. I don't know whether it uses randomness similarly to and as strong as Linux's /dev/random or /dev/urandom. (2) would be cool if mosaic could operate on stdin, or for that matter listen on a socket. (3) You should check to be sure files written in /tmp/xxx on Linux are not ever flushed to physical disk. That could be undesirable. I'm not 100% on this but I believe there can arise a condition that could cause stuff on /tmp in tmpfs to get swapped out to the pagefile - you could work around that by doing swapoff -a or by using ramfs instead of tmpfs. (Ramfs shouldn't get paged out.) Sorry but I'm not familiar enough to say what FreeBSD/Mac do differently, if anything, in this regard. (4) an input file which must be divvied up into sufficiently many chunks will cause non-ASCII characters in your X-Custom-X.... header for some chunks. Whether those get munged by any particular mail server is up to that mail server. (5) date to the nanos on Windows, at least with cygwin, returns a value with the final two digits as zero, always. See (1) supra. (6) it would be a good idea to pad the X-Custom-Xxx: header content to the same length for all output emails. Or to a random length. For the purpose of obfuscating what chunk is a final chunk and, thus, for obfuscating when an end of a transmission of chunks has occurred. (7) Not really MOSAIC as such, but it would be a good idea to make sure the output emails are sent in random order to a random email server. (8) Oald Internet history: https://en.wikipedia.org/wiki/Penet_remailer This is all far more interesting than my daily work. Tue, 10 Mar 2026 16:35:27 -0700 Andy from private IP Reply #12597893 Thanks for the input-- very helpful. We decided to allow up to 676 fragments (26 x 26), but the next release might allow more. Tue, 10 Mar 2026 17:48:39 -0700 doublefriedchicken from private IP Reply #13917374 👍 We are all just a bunch of weird inventors I guess. Thu, 12 Mar 2026 07:33:47 -0700 Andy from private IP Reply #16802331 We updated the script and white paper, and the latest version of the script is even more scary than before. https://www.watters.law/articles/attachments/mosaic/MOSAIC.pdf https://www.watters.law/articles/attachments/mosaic/mosaic.sh Thu, 12 Mar 2026 08:19:14 -0700 phosita from private IP Reply #14660288 👍 Got the new code. Will do the needful and revert, drs Fri, 13 Mar 2026 17:21:04 -0700 Andy from private IP Reply #12819756 Check the latest versions, updated with chunk randomization feature that makes the messages randomly sized and even harder to detect.Replies require login.
@17976678 Andy 👍 @18674056 47.157.45.11 👍 @13917374 Andy 👍 @14660288 Andy 👍
